20 Great Reasons For Deciding On A Zk-Snarks Messenger Website
Wiki Article
The Zk Shield That Powers It: What Zk-Snarks Can Hide Your Ip Address And Identification From The World
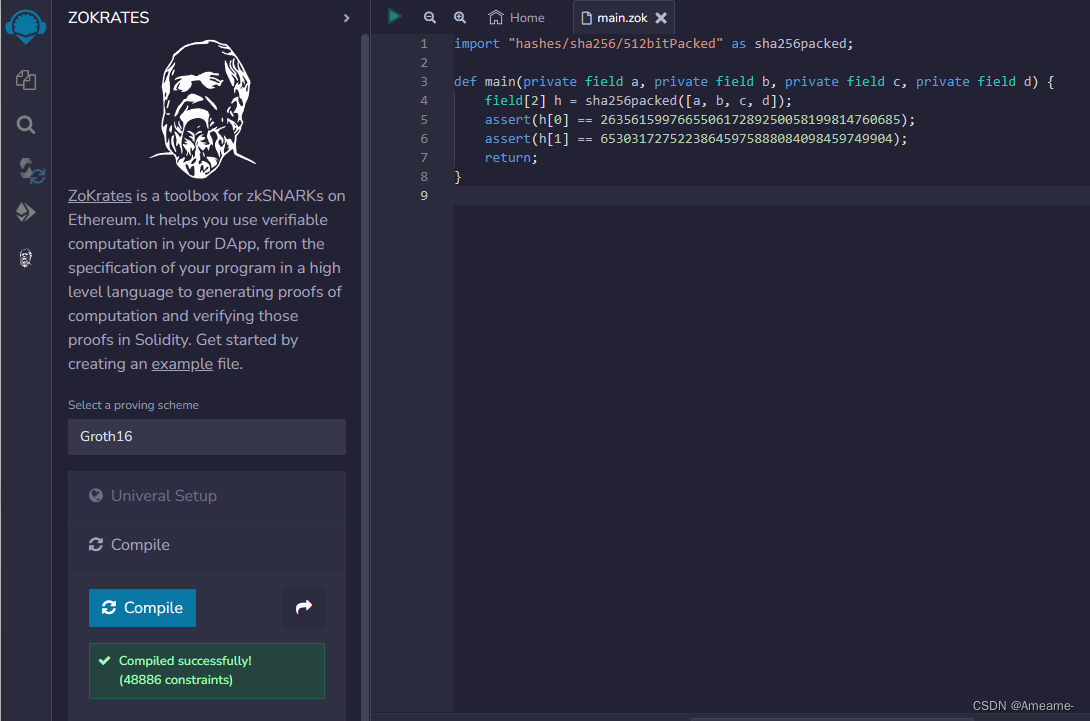
For decades, privacy programs use a concept of "hiding out from the crowd." VPNs funnel you through a server, and Tor helps you bounce around the nodes. These can be effective, but they are in essence obfuscation. They conceal the source by moving it instead of proving it does not need to be made public. Zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) introduce a distinct paradigm that will be able to prove that you're authorized for an action to be carried out without divulging who the authorized person they are. With Z-Text, the ability to broadcast messages to the BitcoinZ blockchain, and the network can verify you are an authorized participant who has valid shielded addresses, but it's unable to tell which addresses you have used to broadcast the message. Your IP address, your identity along with your participation in the conversation are mathematically inaccessible to the outsider, yet legally valid for the protocol.
1. The dissolution of the Sender-Recipient Link
It is true that traditional communication, even with encryption, discloses the communication. Someone who observes the conversation can determine "Alice communicates with Bob." Zk-SNARKs can break this link in full. If Z-Text broadcasts a shielded payment an zk proof confirms you are able to verify that the sender has sufficient balance and the correct keys--without revealing details about the address sent by the sender or the recipient's address. To an observer outside the system, the transaction will appear as a noisy cryptographic signal emanating in the context of the network itself and in contrast to any one particular participant. The relationship between two human beings becomes impossible for computers to prove.
2. IP Privacy Protection for IP Addresses at Protocol Niveau, not the App Level
VPNs as well as Tor safeguard your IP by routing your traffic through intermediaries. But those intermediaries also become new points of trust. Z-Text's use of zk-SNARKs means your IP's location is never relevant in the verification process. When you broadcast a secure message to BitcoinZ peer-to-10-peer system, you are one of thousands of nodes. The ZK-proof makes sure that any person who is observing the network traffic, they cannot correlate the incoming message packet and the wallet or account that has created it. The evidence doesn't include that particular information. The IP's information is irrelevant.
3. The Abolition of the "Viewing Key" Challenge
With many of the privacy blockchain systems in the blockchain privacy systems, there's"viewing key "viewing key" capable of decrypting transaction information. Zk's-SNARKs which are implemented within Zcash's Sapling protocol and Z-Text allows selective disclosure. One can show that you've sent a message without sharing your address, your transactions in the past, or the complete content of that message. Proof is the only evidence shared. The granularity of control is not possible in IP-based systems as revealing information about the source address automatically exposes the identity of the sender.
4. Mathematical Anonymity Sets That Scale Globally
A mixing service or a VPN Your anonymity is restrained to only the other people who are in the pool at that particular moment. By using zk-SNARKs your privacy is ensures that every shielded identifier is throughout the BitcoinZ blockchain. Because the evidence proves you are a secured address, one of which is potentially millions of addresses, yet gives no hint which one, your security is a part of the network. Your identity is not hidden in any one of your peers instead, but within a huge number of cryptographic identities.
5. Resistance against Traffic Analysis and Timing attacks
The most sophisticated attackers don't just look at the IP address, but they analyse pattern of activity. They look at who sends data when and correlate events. Z-Text's use for zk-SNARKs together with a blockchain mempool permits decoupling operation from broadcast. One can create a cryptographic proof offline and broadcast it later and a node could transmit it. The time of proof's integration into a block not directly linked to the instant you made it. impairing the analysis of timing that typically blocks simpler anonymity methods.
6. Quantum Resistance via Hidden Keys
IP addresses do not have quantum resistance If an attacker is able to log your traffic now but later crack the encryption they could link your IP address to them. Zk-SNARKs as they are utilized in Z-Text, shield your keys themselves. Your private key isn't publicized on the blockchain, since this proof is a way to prove that it is the correct key and does not show the key. Even a quantum computer in the near future, will examine only the proof rather than the private key. All your communications are private as the password used to secure them wasn't exposed as a hacker.
7. Inexplicably linked identities across multiple conversations
With just a single wallet seed and a single wallet seed, you can create multiple shielded addresses. Zk'sARKs make it possible to prove that you have one of the addresses without sharing the one you own. It means that you are able to have more than ten conversations, with ten distinct people. But no witness, even the blockchain cannot trace those conversations to the very same wallet seed. The social graph of your network has been designed to be mathematically unorganized.
8. The suppression of Metadata as an Attack Surface
Security experts and regulators frequently say "we don't need any content it's just metadata." It is true that IP addresses represent metadata. The person you call is metadata. Zk's SARKs stand apart from privacy technologies because they hide details at a cryptographic scale. The transaction itself does not contain "from" and "to" fields, which are in plain text. There is no metadata to be subpoenaed. Only the confirmation, and this can only prove that a legal procedure was carried out, not the parties.
9. Trustless Broadcasting Through the P2P Network
When you use the VPN and trust it, the VPN provider to never log. In the case of Tor then you trust the exit network not to watch you. Utilizing ZText, it broadcasts your zk proof transaction to BitcoinZ peer to-peer platform. Then, you connect to some random networks, share the data, and then you disconnect. Nodes are not learning anything, as the data does not prove anything. They're not even sure your identity is the primary source as you might be serving as a relayer for someone else. This network is a dependable service for private data.
10. The Philosophical Leap: Privacy Without Obfuscation
Additionally, zk's SNARKs mark one of the most philosophical transitions that goes from "hiding" in the direction of "proving that you are not revealing." Obfuscation technology accepts that the truth (your identification number, your IP) is a risk and should be kept secret. Zk-SNARKs acknowledge that the truth doesn't matter. The system only has to recognize that the user is authenticated. A shift from passive hiding to proactive irrelevance is one of the fundamental components of the ZK shield. Identity and your IP is not hidden; they can be used for any operation of the network so they're not requested and never transmitted or made public. Read the most popular zk-snarks for more recommendations including encrypted messenger, messenger with phone number, messenger text message, messenger text message, private message app, messenger not showing messages, message of the text, message of the text, messenger with phone number, encrypted text message app and more.
Quantum-Proofing Chats: What's The Reason? Z-Addresses, Zk-Proofs And Z-Addresses Cryptography
The threat of quantum computing is frequently discussed in abstract terms -- a futuristic boogeyman which will destroy encryption completely. In reality, it is nuanced and more urgent. Shor's algorithm if executed on a highly powerful quantum computer, could theoretically breach the elliptic curvature cryptography that makes up the bulk of the internet and bitcoin today. But, not all cryptographic methods are as secure. Z-Text's technology, based upon Zcash's Sapling protocol, and Zk-SNARKs features inherent properties that deter quantum encryption in ways conventional encryption is not able to. The real issue lies in the distinction between what can be seen and what's concealed. By ensuring that your public secrets aren't revealed on the Blockchain Z-Text protects you from anything for a quantum computer to penetrate. Past conversations, your identification, and even your wallet are kept secure, not due to complexity alone, but by mathematic invisibility.
1. The Fundamental Vulnerability: Detected Public Keys
To fully understand why ZText is quantum-resistant first understand why most systems are not. In standard blockchain transactions, the public key of your account is disclosed after you have spent money. A quantum computer is able to take your public key exposed and with the help of Shor's algorithm extract your private keys. Z-Text's secured transactions, employing two-addresses that never disclose their public key. Zk-SNARK is a way to prove you possess the key, without divulging it. This key will remain undiscovered, giving the quantum computer little to do.
2. Zero-Knowledge Proofs for Information Minimalism
Zk-SNARKs, in their nature, are quantum-resistant due to the fact that they depend on the complexity in solving problems that are not much solvable by quantum algorithms such as factoring or discrete logarithms. The most important thing is that the proof itself is completely devoid of detail about the key witness (your private code). While a quantum-computer could in theory break one of the assumptions behind the proof it'd have nothing for it to operate with. It's just a dead end in cryptography that verifies a statement without containing any of its content.
3. Shielded Addresses (z-addresses) as the Obfuscated Existence
The z-address used in the Zcash protocol (used by Z-Text) is never published as a blockchain entry in a way that identifies it as a transaction. When you receive funds or messages, the blockchain only confirms that a shielded pools transaction has occurred. The address you have entered is beneath the merkle's merkle tree of notes. A quantum computer scanning this blockchain is only able to view trees and proofs, not leaves and keys. Your cryptographic address is there, but not in observance, making it inaccessible to retrospective analyses.
4. Defense: The "Harvest Now, Decrypt Later" Defense
The largest quantum threat in the present doesn't involve an active attack and passive accumulation. The adversaries can take encrypted data through the internet, then save it, while awaiting quantum computers' maturation. In the case of Z-Text it is possible for an attacker to be able to scrape blockchains and take all transactions shielded. However, without viewing keys, and without ever having access to the public keys, they are left with no way to crack the encryption. Data they extract is unknowledgeable proofs which, in the end, don't contain any encrypted information that they would later crack. The message isn't encrypted inside the proof. Instead, the proof is the message.
5. The importance of one-time usage of Keys
With many systems of cryptography, the reuse of a key results in more exposed data for analysis. Z-Text is based on BitcoinZ blockchain's application of Sapling permits the usage of multiple addresses. Every transaction can be made using an unlinked, brand new address made from the seed. This implies that even should one transaction be affected (by any other method that is not quantum) it is still secured. Quantum resistance can be increased due to the constant rotation of keys, this limits the strength of one cracked key.
6. Post-Quantum Assumptions In zk-SNARKs
Modern zk stacks frequently depend on equations of curves on elliptic lines, which can theoretically be vulnerable to quantum computer. However, the specific construction employed in Zcash as well as Z-Text allows for migration. This protocol was designed to support the post-quantum secure zk-SNARKs. Since keys aren't divulged, the change to a new proving system can happen at the protocol level, without being obliged to make public their data. The shielded pool design is ahead-compatible to quantum-resistant cryptography.
7. Wallet Seeds as well as the BIP-39 Standard
Your wallet's seed (the 24 words) cannot be hacked similarly. The seed itself is simply a massive random number. Quantum computers are not significantly superior at brute-forcing random 256-bit numbers than classic computers due to the limitation of Grover's algorithm. The issue lies with the derivation of public keys from the seed. In keeping the public keys in a secure way using zk SNARKs, the seed is secure even during a postquantum age.
8. Quantum-Decrypted Metadata vs. Shielded Metadata
Even if quantum computers breach encryption in some ways But they're still facing the challenge of Z-Text hiding metadata on the protocol level. If a quantum machine is able to claim that a transaction has occurred between two parties when they were able to reveal their keys. But if those public keys weren't disclosed, as well as the transaction is only a zero-knowledge evidence that doesn't contain information about the address, then Quantum computers only know that "something happened in the shielded pool." The social graph and the timing and the frequency are not visible.
9. Merkle Tree as a Time Capsule. Merkle Tree as a Time Capsule
Z-Text records messages on the blockchain's merkle trees of the notes shielded. This is an inherently secure structure from quantum decryption, because in order to discover a specific note, you must know its notes commitment as well as its location within the tree. In the absence of a viewing key, any quantum computer will not be able to recognize your note from billions of others within the tree. The computational effort to brute-force go through all the trees to locate a particular note is insanely enormous, even with quantum computers. It also increases with every block added.
10. Future-proofing through Cryptographic Agility
In the end, the primary characteristic of Z-Text's resistance to quantum radiation is its cryptographic aplomb. Because the software is based upon a blockchain-based protocol (BitcoinZ) which is modernized through consensus in the community the cryptographic components can be removed as quantum threats materialize. Customers aren't bound by the same algorithm for all time. As their entire history is hidden and the keys are auto-custodianized, they can move to new quantum-resistant curves but without sharing their history. The architecture ensures that your conversations are safe not only in the face of threats today, yet also for the ones to come.